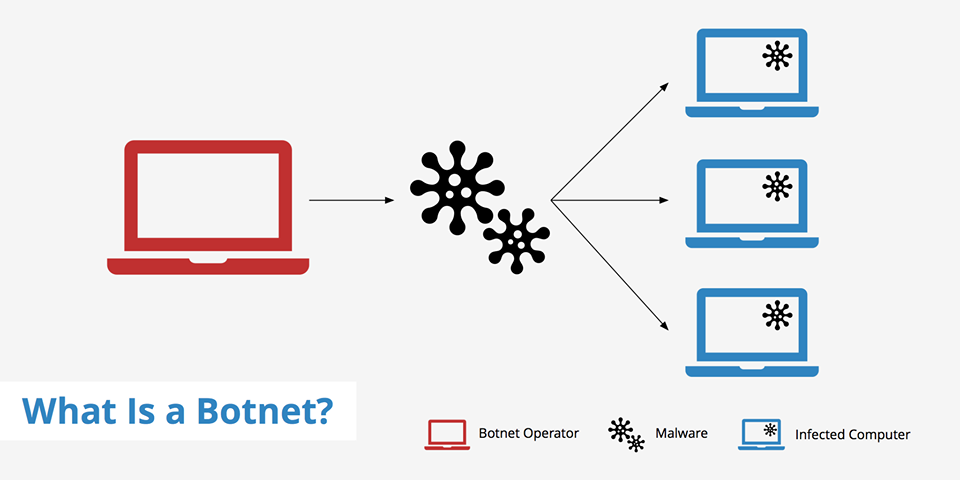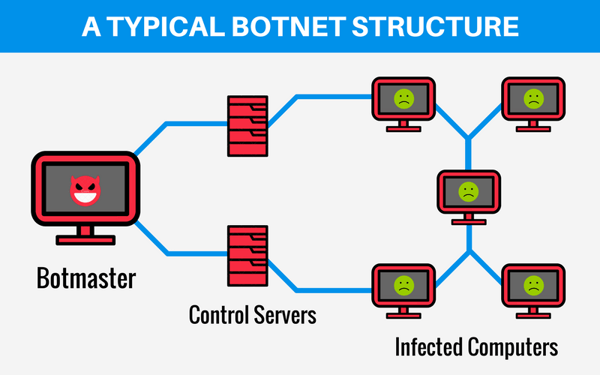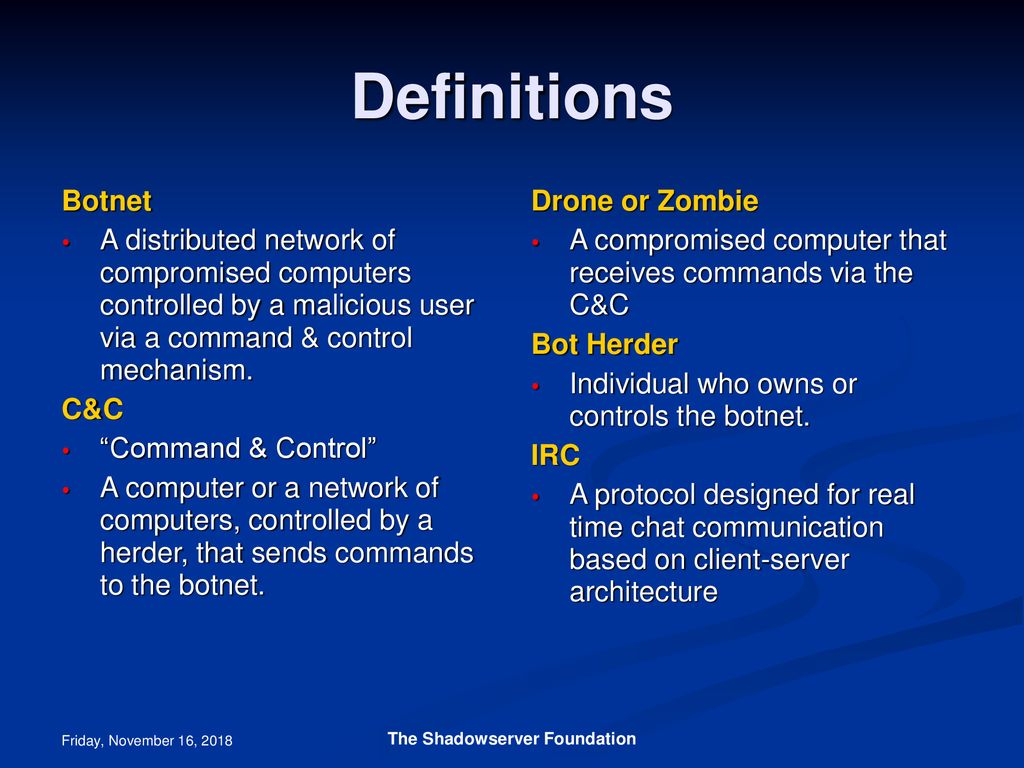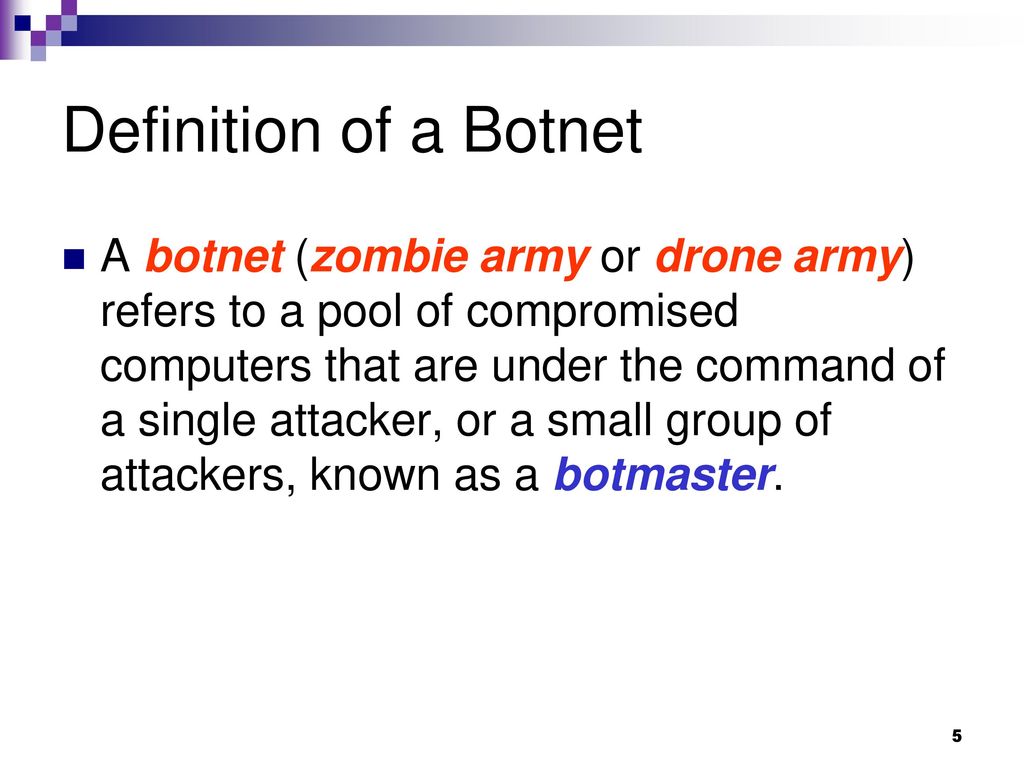
What is a botnet? How are botnets created? How are they controlled? How are bots acquired? What type of attacks are they responsible for? - ppt download

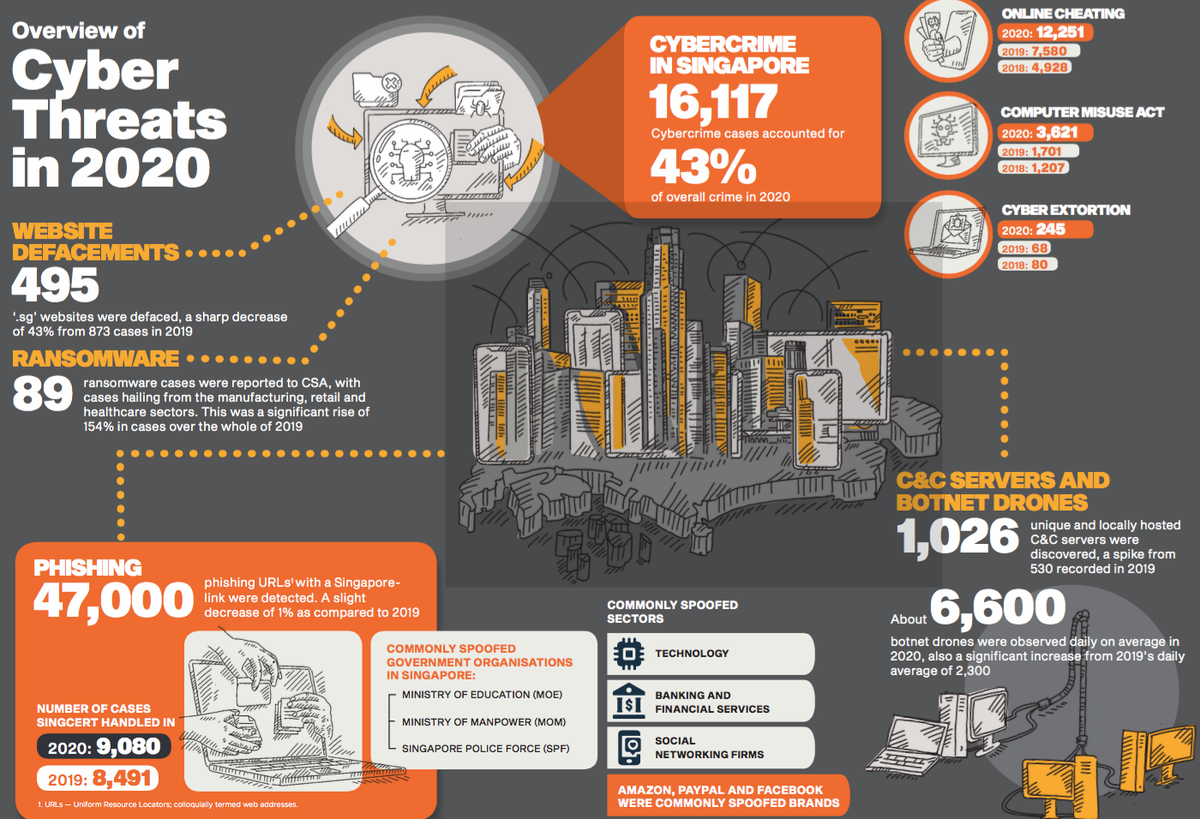
Surge in Singapore-linked 'botnet drones', used by cyber criminals to hack into household devices: Report - TODAY

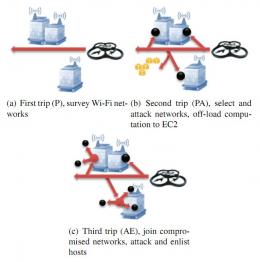
Drones | Free Full-Text | An Intrusion Detection Model for Drone Communication Network in SDN Environment

Deep learning approach for investigation of temporal radio frequency signatures of drones - Sohal - 2023 - International Journal of Communication Systems - Wiley Online Library
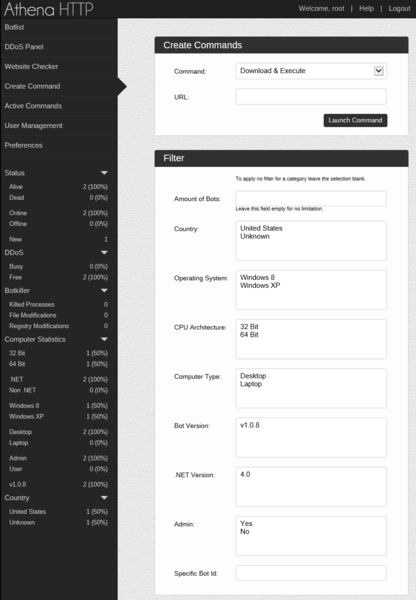
Electronics | Free Full-Text | Exposure of Botnets in Cloud Environment by Expending Trust Model with CANFES Classification Approach

The architectural design of AA-Dense RNN based Botnet attack detector... | Download Scientific Diagram

Information | Free Full-Text | A Botnets Circumspection: The Current Threat Landscape, and What We Know So Far

![Botnet Drone! by Poofdra -- Fur Affinity [dot] net Botnet Drone! by Poofdra -- Fur Affinity [dot] net](https://d.furaffinity.net/art/poofdra/1615251090/1615251090.poofdra_unknown__7_.jpg)